There’s been a whopping big security hole in Microsoft Office for the last 17 years, via the old Equation Editor and a less than vigilant Microsoft. We have details of the problem, how to fix it and why there’s more to come ….
In the November 2017 patches there are some that are innocently labelled “Microsoft Office Memory Corruption Vulnerability”.
Behind that bland and common title lies the story of Microsoft totally overlooking a gaping hole in their security regime. It’s a story worth keeping in mind next time you hear the company talking about their commitment to software security.
Pretty much everyone affected
This security lapse applies to anyone with Microsoft Office because it involves an old component, the Equation Editor.
All versions of Office including the latest Office 2016 (Office 365 subscribers or not).
All versions of Windows.
32-bit or 64-bit.
All languages.
You don’t need to use the old Equation Editor for this security hole to be exploited. You don’t even have to know what the Equation Editor is. Hackers can use the faulty component without any interruption or interaction with the user – just opening a hacked document is enough.
In a masterful piece of Microsoft obfuscation and misdirection, the description of this major problem manages to not mention the core problem nor the embarrassing length of time it’s been there.
CVE-2017-11882 | Microsoft Office Memory Corruption Vulnerability has just standard, bland and non-specific wording. There’s no mention of the highly vulnerable Equation Editor at all. No mention of all the Office versions affected prior to Office 2007.
Similarly, the KB articles for each security patch, like this one for Office 2010, don’t mention the Equation Editor at all.
Old, old software
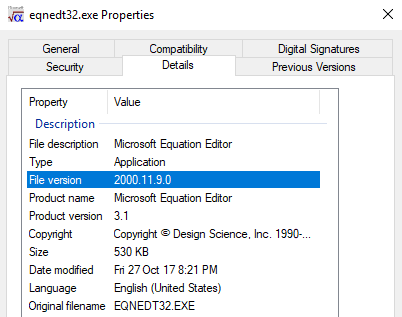
The Equation Editor was revamped for Office 2007 but the older version of Equation Editor was kept for compatibility. Even Office 2016 for Windows still has this old EQNEDT32.exe file sitting among the Office installed files.
Looking inside EQNEDT32.exe confirms that the file hasn’t been updated since 2000 – 17 years ago.
That’s a bad sign. Any old software is likely to have security holes that modern hackers can use to infiltrate your computer.
Just the age of EQNEDT32.exe should have been a warning to Microsoft’s security people. It was a warning that was totally overlooked.
Typically for such an old component, it does things that are verboten in the 21st Century. When you run the old Equation Editor, it makes a new process separate from Office. That process has none of the security protections made for Windows or Office to stop hackers using a sub-system to access your computer.
In other words, the old Equation Editor has been an enormous open door into your computer.
Skeleton in the Closet
Microsoft didn’t find this security lapse, as they should have. It was up to independent researchers Embedi to find it and publish a 20 page report titled ‘Skeleton in the Closet‘
Sure enough, researchers quickly found two memory corruption holes in EQNEDT32.exe that let hackers run other code on a computer.
Fixes
The best thing to do is update Office for Windows. Here’s the downloads and KB reference articles for the Office versions that Microsoft supports.
Office 2007 Service Pack 3 KB4011276 Download
Office 2010 Service Pack 2 (32-bit editions) KB2553204 Download
Office 2010 Service Pack 2 (64-bit editions) KB2553204 Download
Office 2013 Service Pack 1 (32-bit editions) KB3162047 Download
Office 2013 Service Pack 1 (64-bit editions) KB3162047 Download
Office 2016 (32-bit edition) KB4011262 Download
Office 2016 (64-bit edition) KB4011262 Download
If a document is opened with a link to the old Equation Editor, it should raise a prompt to open in Protected View. Best to choose Protected View until you’re sure Office is patched.
Office 2003 and before
Earlier versions of Office are also vulnerable, but Microsoft don’t care about them (sorry, ‘support has expired’).
For those Office releases, there’s an additional Registry key thats reported to stop the old Equation Editor from running.
32-bit Windows
HKLM\SOFTWARE\Microsoft\Office\Common\COM Compatibility\{0002CE02-0000-0000-C000-000000000046}
Compatibility Flags
REG_DWORD
0x400
64-bit Windows (running 32-bit Office)
HKLM\SOFTWARE\Wow6432Node\Microsoft\Office\Common\COM Compatibility\{0002CE02-0000-0000-C000-000000000046}
Compatibility Flags
REG_DWORD
0x400
But wait … there’s more
You can be sure hackers and researchers are now combing Windows and Office for other old components that Microsoft has ignored. Any of them could be a trove of new ways to infect, exploit or ransom your computer.
Embedi suggests some possibilities:
- ODBC drivers and Redshift libraries (compiled without essential protective measures).
- ODBC drivers and Salesforce libraries (compiled without essential protective measures).
- Some .net compilations responsible for Microsoft Office user interface.
So look forward to more patches, more obfuscation and a total absence of embarrassment or apology from Microsoft.
And finally … a video!
Embedi researchers have a video demonstrating the exploit in Office 2010 on Windows 7, Office 2013 on Windows 8.1, and Office 2016 on Windows 10.