There’s very few security patches this month but the major fix is for Word 2016 for Windows.
Alas, as usual, Microsoft tries to overwhelm with a lot of standard phrases leaving key questions unanswered.
This months security flaw is similar to many others over the years. A hacked document can manipulate computer memory to allow an unwanted program to run on the computer.
There are patches for:
Microsoft Word 2016 (32-bit edition)
Microsoft Word 2016 (64-bit edition)
Microsoft SharePoint Enterprise Server 2016
You should not need to click the above links and install individual patches. Office update should update your software automatically.
What type of document?
What’s lacking is important detail, especially what type of Word document/s can take advantage of this exploit. Most likely it’s the older .doc files and it would be more worrying if newer .docx files can be infected.
There’s nothing in Microsoft’s disclosure that covers this vital point. It only talks about a “specially crafted file” or “document”. The information under ‘Vulnerability’ in the security bulletin might look impressive at first glance but it’s just generic sentences that are used over and over again. In fact, most of any MS Security Bulletin is a ‘copy and paste’ job from past bulletins.
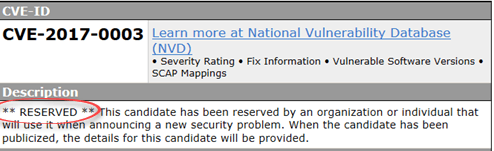
Microsoft provides a link to the external CVE page for the vulnerability, which might have more detail. But that page is currently blank, as it usually is when Microsoft links to a newly disclosed problem.
Microsoft says that the problem is limited to the current users access privileges but it still leaves hackers an opportunity. For example, they could run a program that looks like a virus warning and trick the unwary into allowing greater access.
Critical, sorry, just Important
Microsoft’s self-rating of security flaws has always been a concern. After all, it’s in Redmond’s interest to downplay the severity of any problem. This month’s flaw in Office looks like it was ‘revised downwards’ after it went public.
Security bulletin MS17-002 was originally rated ‘Critical’ but was quickly downplayed to ‘Important’.
With little hard information about the flaw, it’s hard to judge which rating is more appropriate.