While Microsoft is busy patching for the Spectre/Meltdown chip flaws there’s another serious and more easily abused security flaw in Word. It’s fairly simple and not yet detected by any of the anti-virus programs.
It’s called ‘SubDoc’ and was discovered by Rhino Security Labs who have gone to the extent of creating a tool to let people test the bug for themselves.
SubDoc
A Word document can contain a link to another Word document. It lets the content of one document be embedded in another. Use it, for example, to include some standard wording into a bigger contract.
Anyone who uses Word’s Master Documents will be familiar with sub-documents. The master document has a series of links to individual documents (eg the chapters in a book).
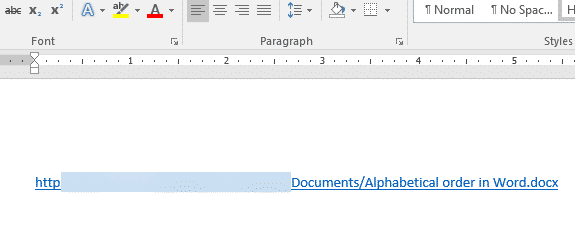
Normally those linked documents are on the same computer or network but the link can be to any place on the internet. Here’s a Word document with a link to a document somewhere on the Internet.
All that’s OK if the sub-document is real but what if it’s not really a Word document at all, instead it’s a ‘listening post’.
Rhino rigged up a web server that would read Word’s attempt to get the sub-document. That attempt can reveal a networked computers login credentials in clear text or SMB request with NTLMv2 hash
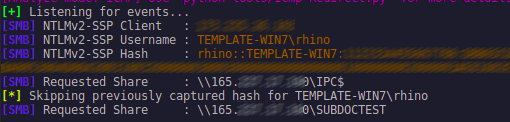
Source: Rhino Security Labs
The key problem is that organizations should have filter in place to stop outgoing SMB calls, but many do not. Microsoft will call this a ‘mitigating factor’.
All a hacker has to do is trick people into opening a Word document and clicking ‘Enable Editing’ to exit protected mode. People are conned into doing that every day, despite all the warnings and software protections.
The Word document can be in the newer .docx format unlike many Office exploits which need to use the older .doc formats.
When the Word attachment is fully opened, Word attempts to grab the linked document right away. No clicking or extra permission is requested, Word does what it’s supposed to do. The hackers can hide the link so it’s not even visible to the user and they don’t know what happened.
Meantime the hackers grab the NTLMv2 login details and gain access to a network.
What to do?
This is Word acting as it’s designed to do, so anti-virus software are not checking for it. Fixing this problem isn’t easy because it’s not a true security bug, rather a way to exploit a useful Word feature.
Hopefully, Microsoft and the AV firms will start checking for sub-documents links with http prefixes or external SMB links and pop-up a warning?
Microsoft should consider some additional safeguards for linked documents outside the computer or local network. Those types of links are relatively unusual because Word slows down a lot when linked to a document across the Internet.
Organizations should protect themselves by filtering SMB calls to the outside so the NTLMv2 credentials don’t get out.
Individuals should keep doing what they’re always told. Be very careful of unexpected documents no matter how they arrive via email, messaging, USB stick, CD/DVD, carrier pidgeon, transporter beam, whatever.
Details
All this is documented in a Rhino Security Labs posting.
SubDoc Injector
Rhino Security Labs and Hector Monsegur have created a Python tool that will make an example document with the embedded link. The code is designed so administrators can test their systems.