Hackers continue to trick people into giving away their Office 365 login details with a little help from Microsoft. The criminals are getting cleverer by not only stealing passwords but checking immediately and hiding the theft while they copy your mailbox.
Avanan has the details on this latest type of Office 365 phishing. It starts normally enough with a fake email maybe a sincere looking quarantine notice.
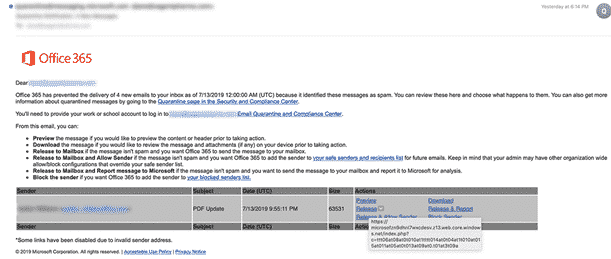
Source: Avanan
Click on the bogus link leads to a fake login page hosted on a Microsoft site with a Microsoft secure certificate!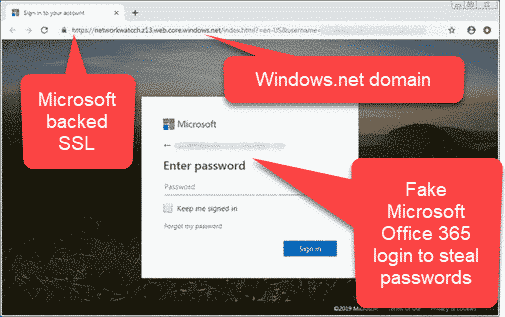 A fake Microsoft login page, hosted by Microsoft with a Microsoft SSL certificate!
A fake Microsoft login page, hosted by Microsoft with a Microsoft SSL certificate!
What happens on the fake login page is new. In the past, the phishing pages just accepted whatever you typed in. The page didn’t check your login and gave the same fake response page no matter what. If wary of a login page, test it by typing incorrect login details.
Now, the hackers are immediately checking the stolen name/password to see if they are correct. That happens within seconds. If wrong, they show the page again just like the real Office 365 site.
The phished name/password are tested automatically using the IMAP email connection. If the hackers code can get into your mailbox, they start copying your entire mailbox just a few moments after the ‘Sign in’ button is clicked.
Meantime, the tricked user sees their outlook.office.com web mailbox. They have no idea they’ve been hacked. Meantime the criminals are getting a copy of all your emails and attachments.
The immediate checking of name/password by the fake login page means that one part of security training doesn’t work. Staff are trained to first test a login page by entering wrong details and see what happens. That might not work when the hackers are real-time testing the login and showing different web pages.
What to do
There are two preventative measures for Office 365 users and admin to do. Meantime the silence from Microsoft is deafening and hurting their customers.
Disable IMAP
If IMAP email connections are NOT necessary, disable that option. IMAP is rarely used these days because Exchange ActiveSync is available in all modern devices.
Admins can do it for all users via PowerShell then selectively enable if a user really needs it. Admin controls for each user are at Recipient | Mailbox Features then scroll down to IMAP and click Disable.
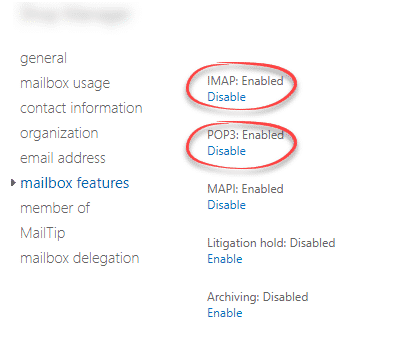
Maybe also disable POP since it’s also rarely needed these days.
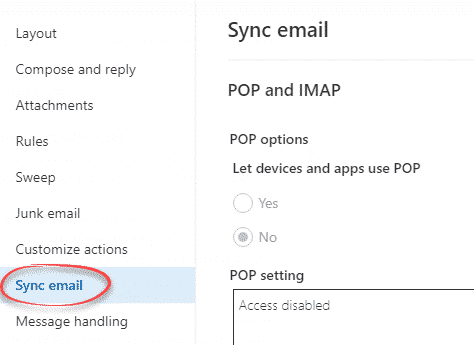
As an Office 365 user, go to Setting | Sync Email to see the current POP and IMAP setting. If greyed out, it means your Admin has control. If not, you can set ‘Let devices and apps use POP’ to off.
Enable MFA aka Two-Factor Authentication
Yes, we’re harping about Two-Factor Authentication again <sigh>.
This and many phishing and hacking attacks can be stopped by setting up two factor authentication.
That applies not just to Office 365 hosted accounts but any Microsoft / Outlook.com, Google/Gmail and other important logins.
Our ebooks Windows 10 for Microsoft Office users and Office 365 for Windows: Straight Talk both have chapters that take you through the steps to setup Two-Factor Authentication.
Microsoft, where are you?
Microsoft loves to boast about their commitment to security, yet they continue to allow hackers to host their fake logins on Microsoft servers on the windows.net domain AND a Microsoft backed SSL certificate.
That needs to change. New Azure hosting should have a default hosting domain and SSL that has no connection to Microsoft, Windows or Azure.
It might be hard for Microsoft to check all the many Azure hosted pages but some of their much-hyped AI should be made capable. At the very least, check for pages and supporting code hosted on Microsoft’s site.