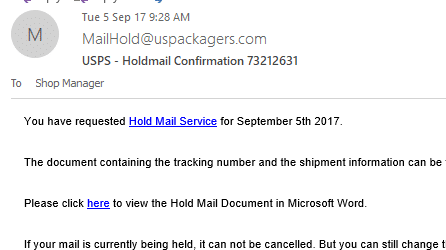
Here’s the latest hacker email we’ve received, a good example of a phishing and infected Word document email. We’ll use it as an example what to watch for and avoid.
This message got through various anti-spam filters to arrive in the Office Watch managers Outlook 2016 Inbox.
Which brings us to the first important point
Place NOT thy trust in spam and phishing filters
Your mail host has spam and phishing filters in place and maybe you’ve got your own email checkers running too … that does NOT mean anything that arrives in your Inbox is ‘OK’. Far from it. Be suspicious of any strange or unexpected message.
(Aside from not being 100% perfect, anti-spam filters have a less known problem. They can block legitimate messages you really want to see.)
What made us suspicious?
The ‘From’ address wasn’t the US Postal Service usps.com but some other domain. Uspackagers.com looks like a legitimate company and probably the MailHold@uspackagers.com address is a fake designed to trick the unwary.
The formatting looks wrong. The very top of the email is mostly blank space and then a poorly formatted heading.
We don’t have any ‘Hold Mail’ service pending. Irrelevant emails are a giveaway of a fake. If the email is from a bank you’ve never dealt with, it’s a fake and deserves immediate deletion. Even if the message is from a bank or company you use, it still might be a fake.
Check the links!
Before clicking ANY link in an email, check what the link really is – not just the visible label.
Outlook for Windows makes that easy, hover your mouse over any link and the actual web address will show in a tooltip.

The first link in the message is legitimate (It will take you to the real USPS Holdmail site) but it’s a trick to lull you into a false sense of security.
The second link is the trap, the web link has nothing to do with USPS.
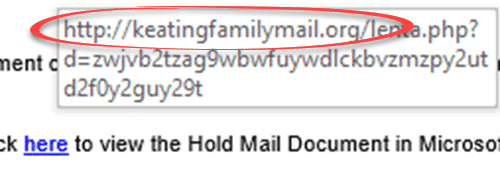
The text tells you that the link will open a Microsoft Word document. That’s will trick people into opening the document. Savvy computer users should take it as a warning NOT to click the link at all. NEVER open Office documents from emailed links unless you’re very sure of the source.
Don’t blame the (supposed) messenger
The US Postal Service is NOT to blame for this or other fake messages. Some people wrongly blame regular spoofing targets like paypal.com etc. for the fake messages sent in the company’s name.
No person or organization wants their name used to infect computers. You can reduce the risk of spoofing but no way to prevent it completely.
SPF or Sender Policy Framework is a way for domain owners to indicate which mail hosts are allowed to send messages. Anti-spam systems use SPF to see if an email comes from a legitimate source or not.
Uspackagers.com does NOT have an SPF record in their domain setup. That’s probably why the spammers chose the domain for the fake ‘From’ address, in addition to the similar name to USPS.
Anyone with their own domain name, business or personal, should have a SPF record. SPF reduces the risk of your domain being abused by hackers and makes it more likely that your real emails will be delivered.