A new report from Sophos shows how hacking via Office documents has changed of lot in 2018 with new attacks coming much faster than in the past.
Microsoft’s assurances that a security bug (sorry ‘exploit’) hasn’t been used ‘in the wild’ doesn’t mean a lot.
Office document hacks made in bulk
The people who find security holes in Windows/Office and make code to exploit those bugs aren’t the people who are trying to get into your computer or network. They sell ‘off the shelf’ tools to criminals.
Most modern hacking attempts are made with ‘builders’ which create Word, Excel, PowerPoint, RTF or PDF files with selected Office and Windows exploits. The hacker just adds their preferred text and look for the document then lets the builder do all the hard work adding nasty code to infiltrate an unprotected machine.
For US$800 a hack builder called Threadkit can be had from a Russian group. Threadkit alone is responsible for about a third of Sophos’s 2018 detections.
2018 is a year of change
This year has seen a major upheaval in these builder packages. Hacking emails went out using a range of exploits, but improved security and detection meant those attempts were becoming less successful. Usually the exploits available from builders adapt slowly over time. Iin 2018 there was a wholesale dumping of old exploits and targeting of newer Office/Windows security lapses.
“We’ve never seen such a radical abandonment of existing exploits (and, in some cases, of the tools that implement them) in such a short period of time.”
Equation Editor exploit
Back in November 2017 Microsoft disclosed a truly embarrassing security bug that had been available for 17 years. A security hole in the old Equation Editor part of Office. So old that Microsoft seems to have lost the original source code.
At the time, Microsoft assured everyone that the exploit had not been seen ‘in the wild’, meaning it had not been used to attack anyone’s computers. Redmond loves using that phrase because it appears to get them ‘off the hook’.
Almost a year later that Equation Editor ‘not seen in the wild’ security bug is now used in over half of attacks worldwide. Officially called CVE-2017-11882, Microsoft’s lapse in securing the Equation Editor is now responsible for 56% of exploits ‘in the wild’.
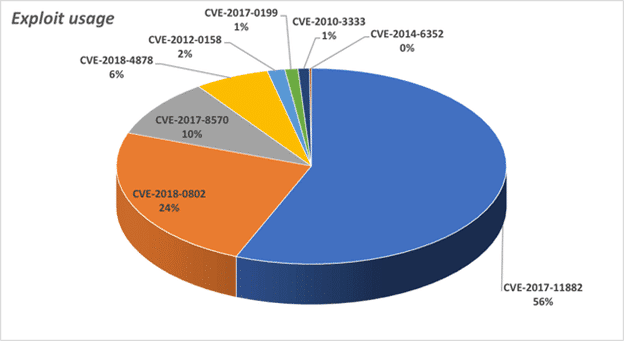
Source: Sophos
Hackers are using this exploit because there are so many unpatched computers out there and it doesn’t need macro/VBA access.
“… the criminals seem to think that the mere availability of patches doesn’t mean that people will install them, and they may be right.”
Security bugs are exploited faster
Sophos also notes another important change in cyber attacks. The delay between a security bug being discovered and criminals using it to attack has dropped from months or weeks to a few days.
” …fresh vulnerabilities quickly make their way into the builder ecosystem.”
For Office and Windows users that means there’s less time to delay in patching computers.
That would not be a problem if Microsoft could be relied upon to produce security patches which didn’t cause even more problems. Cautious Microsoft customers prefer to delay applying new security patches
See the Sophos blog post for more detail.