Here’s how to block .IQY web queries in Excel that are being used to infect machines with Buran ransomware. Yet again, a mostly forgotten part of Office is being used by hackers to get inside computers and networks.
Suspicious Link (great name) found this nasty in an email. It pretends to be a forwarded message with a tiny attachment to print.

Source: Suspicious Link
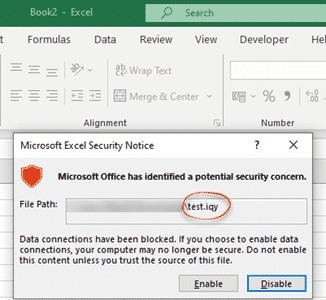
The attachment is an .IQY file which is opened by Excel. There should be an automatic warning for any .iqy file.
But instead of running a web query to add data to a worksheet, the IQY file runs a PowerShell command to download and run a program on your computer.

Source: Suspicious Link
The download is the Buran ransomware which will encrypt Windows desktop and server computers unless a ransom is paid. More on Buran ransomware below.
Protect yourself against .IQY files in Excel
By default, Excel will open .iqy files after the warning above.
.IQY and similar files can be totally blocked from File | Options | Trust Center | Trust Center Settings | External Content.

Check the box ‘Always block the connection of untrusted Microsoft Query files (.iqy .oqy .dqy and .rqy)
Really, that option should now be ON by default at installation. MS Query files aren’t that commonly used and the risk is too high.
Group Policy block
Administrators can apply the same Excel block via Group Policies. Microsoft very quietly released new GP templates here. There’s nothing on the download page to explain what the new templates will do for Office 365, 2019 or 2016 admins.
Email blocking
Microsoft is now blocking emails with .iqy attachments for Outlook.com and Office 365 hosting.
Guess where Buran ransomware came from?
There are two peculiarities about Buran ransomware.
It’s sold as a online service. The makers offer the software to hackers who distribute the ransomware anyway they can (like the .IQY email above). The Buran makers and the hackers share the ransoms with Buran taking a 25% cut.

The notice that appears after a Buran attack. They even have the gall to warn people affected might ‘become victim of a scam’, very cheeky.
“Installed protection against launch in the CIS segment”
The other interesting thing is who is NOT affected by Buran ransomware. Systems in Russia, Armenia, Belarus, Kazakhstan, Kyrgyzstan, Moldova, Tajikistan, Turkmenistan, Ukraine, and Uzbekistan will not run Buran. In other words, the post-Soviet CIS countries.
Knowing that, it’s little surprise that Buran is promoted on Russian underground sites with ‘ads’ like this.

Tips of the virtual hat to Suspicious Link and GBHackers.