How can you send an Office document safely and securely to another person? A simple question with no simple answer.
Who you are guarding against? A random snooper at the recipient’s end who accidentally finds the document, or someone targeting your or your data, such as a commercial rival, nosey journalist, law enforcement, the NSA?
It also depends on the abilities and amount of trouble you and the receiver are prepared to go through. Later on we’ll have some tricks to use however you transmit the Office document.
USB memory stick
Ideally, you put the document on a memory stick and hand it over.
Simple and secure … unless you lose the memory stick. Don’t think it can’t happen to you. UK government officials have been caught leaving sensitive data on train seats.
Something like BitLocker to Go (available in high end versions of Windows) or a free tool like DiskCryptor will stop anyone reading the entire ‘stick’ without a password. Some memory sticks come with security software.
Encrypted Email
If you and the receiver have exchanged digital certificates for email, you can send encrypted emails with attachments.
Digital certificates and email encryption are possible in Outlook, but quite clumsy and difficult. Privacy and Security with Microsoft Office takes you step-by-step through setting up and using encrypted email in Outlook.
The problem with email, encrypted or not, is that it passes through at least two other computers before reaching the Inbox. The message could be read on any of the ‘middleman’ computers or while being sent between them.
Instant Messaging
This is where Instant Messaging (IM) comes in. Depending on the IM software, messages go through a single server only. Ideally the messages are encrypted by the sender’s computer and can only be read by the receiver’s computer.
Sadly, most IM services don’t take privacy very seriously. They make all the right noises but that’s all. Popular IM services like Skype, Skype for Business (Lync) and WhatsApp don’t make your messages private at all. The contents of your messages can (and sometimes are) read by the company. Don’t even think about using those services for exchanging any kind of private information.
For secure IM you need a service which truly takes privacy seriously and the leader in that field is Wickr followed by Telegram (especially their Secret Chat feature).
Which one?
Our preference of all the above options is a secure Instant Messaging service like Wickr or Telegram. They have good security (to a fault in the case of Wickr) and are easy to use on a variety of computers and devices.
Encrypted email is OK but hard to use. Alas, Microsoft shows no interest in making it easier
Shared Folder
If you’re regularly sharing files with a person or team then some type of secure, shared folder might be better. Sadly there aren’t too many choices available.
BT Sync lets you share folders on a ‘peer to peer’ basis directly between computers and devices. There are some technical concerns about the security of BT Sync v2 that haven’t been satisfactorily addressed. It’s a good choice provided you Deselect the ‘Use relay server when required’ option for each share.
SpiderOak is the only truly secure cloud storage service we’re aware of.
If you’re even slightly concerned about your privacy don’t consider the mainstream cloud storage providers. OneDrive, Google Drive, DropBox etc aren’t truly secure at all. Files saved on those systems can be accessed by all manner of organizations.
ALWAYS DO
However you send an Office document, there are some simple tricks to make it harder for most people and organizations to read it.
Password protection
However you send the file, password lock it before sending. File | Info | Protect Document | Encrypt with Password
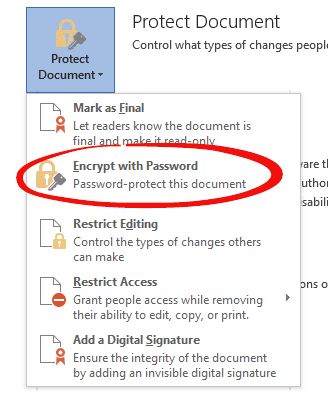
And make sure you give the receiver the password by a separate, secure means. Most likely a simple phone call or secure IM.
Don’t email a password locked file with the password in the email!
Even if someone gets the document (despite the steps you’ll take) they’ll have to get past the password. Password locking an Office document is easy to do and hard to unlock without the right passcode.
Obfuscation
A simple trick is to make the document look less important than it really is.
For example, don’t send a file called
End-of-year Financial Statement - Secret and Confidential.xlsx
that’s bound to attract attention. Instead give it an innocuous name, possibly something out of date, and different extension:
Xmas Party plan.docx
Old keynote draft.pptx
2010 staff piccie.jpg
As long as the receiver knows what the real name or file type is (discuss by phone) they can rename and open it.
Changing the extension makes it harder to open. A determined hacker will look in the file and figure out the real file type. But most snoopers aren’t that determined, they’ll just try to open the file normally, it’ll fail because the extension is wrong and they’ll assume the file is corrupt.
DON’T EVER
Don’t share via any public cloud service including OneDrive, Google Drive and Dropbox, if privacy is important to you. Quite aside from the hacking possibilities, there’s the chance of someone in the company access the files or making them available.
We know for certain that, at the very least, the file name, date, size, sending details etc are sent to the US government by Microsoft, Google, Dropbox and other major cloud storage providers.
Don’t send via standard email. Email messages pass through various computers before reaching the final Inbox and could be intercepted at any of those points.
Don’t use open, unencrypted Wifi. Any open Wifi connection can be ‘snooped’ for data passing between your computer and the access point. This includes email plus file uploads/downloads.
Don’t send via standard instant messaging. We know that Skype instant messaging is intercepted by Microsoft. The popular WhatsApp messenger has some privacy concerns and is certainly not encrypted.
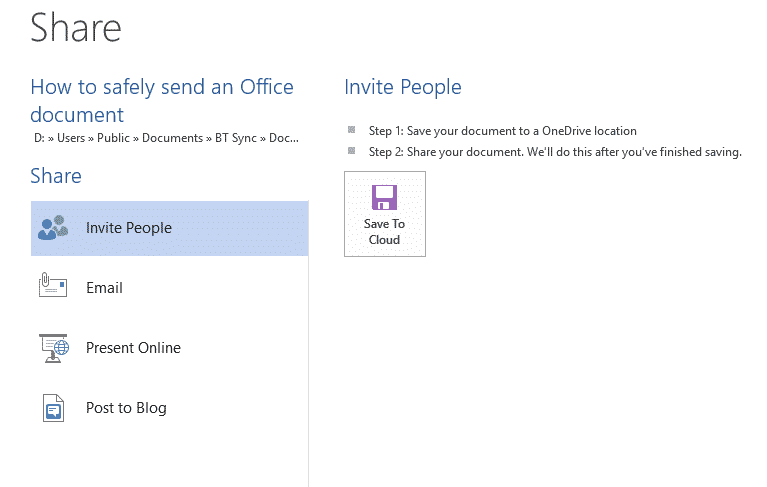
Don’t use any of the Microsoft provided options under File | Share because none of them are secure. If you’ve gone to the trouble of setting up encrypted email then the email is OK, but otherwise don’t bother with the Share choices.