Without any warning, Microsoft stopped their new macro blocking system (called MOTW or Mark of the Web). Now Office for Windows is less secure without customers getting any warning.
UPDATE: the whole ‘on again, off again’ saga continues. On 20 July 2022, Microsoft resumed rollout of the MOTW and Office macro blocking.
Back in February, Office-Watch.com told you about a new system for blocking external documents with macros. That’s the type of document likely to be sent by a hacker or criminal.
The system meant that Windows 11 or 10 would give incoming documents a special tag called MOTW or Mark of the Web. MOTW indicated that the file came from some external source such as an email attachment.
Any document, with a MOTW attribute can’t be opened in Office without a lot of difficulty … deliberately.
Office 365 for Windows got this new protection in June 2022 during a Current Channel update for enterprise users.
Now in early July 2022 Microsoft has quickly reversed course and Office for Windows apps revert to the old behavior where users could easily bypass the warnings to open a macro enabled document. In other words, making Office LESS secure.
What’s worse, there was no prior announcement or proper warning. Unless users and admins are paying close attention, the Office software became more vulnerable.
The change of policy is only temporary. Microsoft has now dropped the magic word ‘temporary’ into
Why the change?
All Microsoft is saying “Based on feedback, we’re rolling back this change from Current Channel”.
Which is probably weasel words for “some of our largest customers hated this change so much, we’ve been forced to disable the new protection in a big hurry.” or “there’s a major bug in the system“
That’s embarrassing for Microsoft who presumably had warnings about problems during the 4+ months the MOTW feature was being previewed.
Like any other time Microsoft is caught out, the company tries to hide their mistake.
There was no advance warning, let alone a proper disclosure. Admins got a partial notice on 7 July if they are watching the Microsoft 365 Admin Message Center (look for
MC322553 (Updated) Microsoft Office default change – Blocking VBA macros in files from the internet )
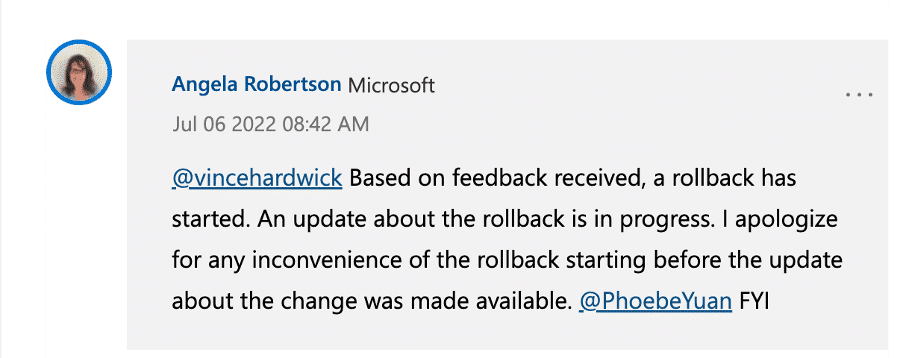
However, the reversion happened before that message. We know because on 6 July (day before) Vince Hardwick posted a question in the comments below the original blog that announced the change.

BIG kudos to Angela Robertson at Microsoft who wasted little time (9 minutes!) in confirming that the rollback was happening AND acknowledging that the change was happening BEFORE proper notification.
Now if Ms Robertson understands the implications for customers — why can’t Microsoft act more quickly?
At the very least, update the original blog post (last tweaked in April 2022) with a prominent note that more secure Office is being delayed (thought Redmond will use a different phrase!). UPDATE: Microsoft has now, belatedly, done that with a note atop the blog post, suspiciously dated 8 July. The other documents have still not been updated and still show the cancelled rollout schedule.
Who is affected?
What’s notably missing from the few Microsoft mentions is which versions of Office (specifically Word, Excel, PowerPoint, Visio, and Access) are affected.
In other words, how to tell if the MOTW protection is on or off?
Microsoft is silent even on that basic point … Grrrrr.
What’s the problem?
We have to wait until / if Microsoft explains what has happened. At the moment all we know is that there are a lot of confused paying customers (our underline since Microsoft seems to overlook that important point) and security experts.
Our guess, it’s just a guess, is that there’s some major bug with the macro blocking feature.
Why? If some big customers didn’t like the new macro blocks, they have the option to disable the feature via Group Policies. Those policies are well documented and available to any enterprise admins.
Microsoft could have changed the rollout, making macro blocking optional in the June 2022 Current Channel for businesses to turn on (Group Policy again). That’s instead of forcing the change on all customers then withdrawing it summarily.
Since administrators had options to bypass the new MOTW macro blocks, we’re thinking that Microsoft’s references to ‘feedback’ might not be refering to displeasure at the feature but rather some more fundamental problem or bug.
In Microsoft’s history there are plenty of occasions when during the preview and testing there were warnings of oncoming troubles. Warnings that were ignored. This could be another example.
Customer deserve a full explanation for this debacle … but don’t hold your breath … that’s not the Microsoft way.
Good stuff now and coming changes to Office.com
New defence against an old problem, Excel XLM Macros