All about Microsoft’s latest Office macro protection feature to stop virus infected documents loading nasties onto a computer. Mark of the Web MOTW is a relatively new way to protect your machine.
Over 2022, a new layer of macro protection was added to Microsoft 365 for Windows. It’s something new in Windows that Office apps will pick up as a warning that a document has been sourced from the Internet or unreliable location.
New Office macro block – In short
Office VBA macros in Office documents from the internet will be blocked by default.
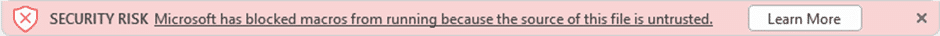
Blocked means you won’t be able to enable the macros directly. Instead of an ‘Enable Macros’ warning you’ll see a red blocking bar like this:
The document, workbook or slides can still be read, it’s only the attached macros that won’t work.
The ‘Learn More’ link goes here to explain the dangers of unknown or Internet sourced documents plus how to unblock a document’s macros.
As presented, the new check is a good thing. Some might be surprised that it’s not in Office already because there’s already warnings about ‘external’ content. This new feature is different and hopefully more secure.
Some of the headlines are flat out wrong. For example, Office will not be disabling all macros by default. The new protections only apply to Office for Windows and only start implementation in April 2022.
As usual, the devil is in the detail and, boy, is there a lot of detail. Important stuff to know and unknowns yet to be disclosed.
Blocking macros not Warning
The key difference is that macros are blocked from running under the new scheme. Unblocking the macros isn’t simple in fact it’s deliberately difficult.
At the moment, suspicious documents get a warning which is too easily bypassed with a single click. Criminals use all sorts of tricks to fool people into clicking Enable Macros.
Mark of the Web or MOTW in Windows
At the heart of this protection is the Mark of the Web or MOTW.
Mark of the Web is something done by Windows (not Office) to tag incoming documents as coming from the Internet, an untrusted or Restricted Zone.
MOTW isn’t saved with the document, it’s a new file attribute saved in the NTFS file system alongside other long-standing attributes like Read Only, Date Created, Date Modified etc.
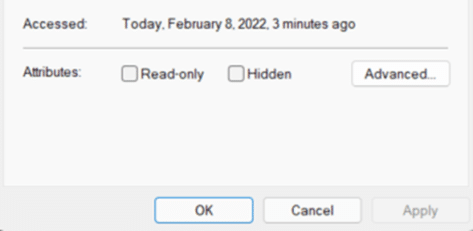
This attribute will show up in the Explorer properties at the bottom of the General tab under the ‘Security’ label.
The MOTW flag is already in Windows 11, Windows 10 and modern Windows Server like this:
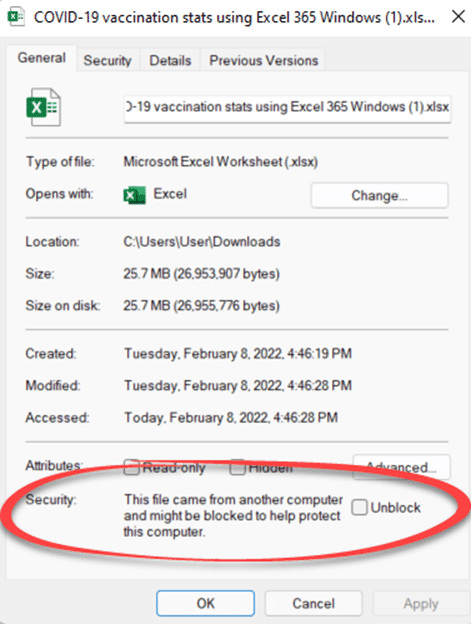
The Properties | General | Security area only appears if the MOTW attribute is set ON. If MOTW isn’t set, there’s just an empty space.
Office and the Mark of the Web
Office for Windows software will look for the Mark of the Web, MOTW when opening documents.
IF the MOTW is present …
- block the macros from running (see warning image above) unless …
- the document is in a Trusted Location OR
- is digitally signed with a Trusted Publisher certificate OR
- was previously opened and ‘Enable Content’ was selected (in other words the document was previously Trusted).
How Office does now and will decide to run macros
Microsoft has a flowchart to explain the process that Office runs to decide whether to enable a macro or not. The upcoming additional check is at right.

Which versions of Windows?
Which versions of Windows will add the Mark of the Web ‘MOTW’ flag? You’ll need:
Windows 11 – all releases have MOTW
Windows 10 – all now supported Windows 10 releases.
Not Windows 8.1 – does NOT have MOTW.
NTFS only
The MOTW flag is only available on NTFS formatted drives, that covers the vast majority of Windows computers because NTFS has been the default format for some years.
FAT32 drives, commonly used be external drives are NOT covered by the MOTW feature.
Microsoft hasn’t mentioned their own ReFS disk format, used on Windows Servers and supported (though rarely used) with Windows 10 and Windows 11. Since ReFS is Microsoft technology, the company should disclose if MOTW is or will be supported.
Office for Mac and smartphone users aren’t helped at all by this new protection.
Which versions of Office?
All the talk has been about Microsoft 365 / Office 365 for Windows.
The new macro blocks apply to Word, Excel, PowerPoint, Access and Visio.
Microsoft is promising the Mark of the Web protections will be added to Office LTSC, Office 2021, Office 2019, Office 2016 and Office 2013 at some ‘future date to be determined’. Presumably only if running Windows 11 or Windows 10.
When is this happening?
The Microsoft Office 365 element of MOTW was rolled out from mid-2022 through to early 2023.
That assumes the underlying Windows 10 version has been updated to include the MOTW check. All Windows 11 releases have MOTW.
And that timetable only applies to Microsoft 365 for Windows. Not Office for Mac, Android, iOS or the web.
More info
Microsoft has published fairly complete information on Mark of the Web and how it’ll work with Office.
The most useful page has the bland title Macros from the internet will be blocked by default in Office. It has details on the release schedule, Group and Cloud policy options.
Discover Office Scripts, the new way to automate Office
New defence against an old problem, Excel XLM Macros
Easy Office document hacking with VBA Stomping or Purging
Why Old Office documents should be banned