There’s so much information and mis-information about the Spectre and Meltdown chip problems, we’ve decided to have a look at what Windows and Mac users need to do about Spectre/Meltdown, what not to worry about, plus some trivia and nerdy details.
A quick What to Do that quickly tells you how to update your computer, Windows, Mac or Apple iOS.
We’ve sorted out the facts from the promises, vague statements and outright guessing:
Windows 10 updating in detail including the two ways to tell if your computer has been patched and the doubt about the current Spectre/Meltdown patch.
Similar coverage for Mac computers.
Other parts of your computer also need updates: Browsers, Anti-virus software, Virtual Machines , computer firmware and that little thing called Microsoft Office!
Cloud computing is especially affected by Spectre/Meltdown.
We’ve also got some nerdy technical details for anyone who’s interested.
Finally, if the Spectre/Meltdown news is giving you a sense of déjà vu, we might know why.
Work in progress: As we find out more, we’ll update this page. As soon as Office-Watch.com knows, we’ll update here.
What are Spectre and Meltdown?
Most security issues you hear about are software flaws, mistakes in Windows, MacOS and programs like Microsoft Office. The software errors are a doorway that hackers can use to take control of your computer.
Spectre and Meltdown are different, they’re hardware bugs. The CPU chip at the heart of most computers has bugs which allow hackers to take control of a computer. We won’t bore you with details, but the chip bugs relate to how memory is allocated and protected.
The risk of Spectre/Meltdown
The immediate risk to computer users is fairly low because the details of both Spectre and Meltdown have been kept secret.
The people who discovered the problems notified Intel, Google, Microsoft and other first. The companies have a chance to patch the bugs before the vulnerability becomes publicly known.
At this stage, the technical details of Spectre and Meltdown have been kept secret. But eventually those details will leak or be re-discovered by baddies. When that happens, there’ll be a new set of attacks aimed at not patched computers.
The Spectre/Meltdown case reminds us of Y2K approaching the millennium. A lot of work went into preventing Y2K affecting computers with some people saying it was overkill and a waste of money. There’s little doubt that hackers will be able to exploit Meltdown and probably Spectre, it’s only a matter of time. In the meantime, we’re always skeptical of the tech industries hype.
Hence the recommended to patch all your computers NOW.
Do it before the hackers catch up.
What to do about Spectre/Meltdown – short version
Happily, the update process is simple. In fact, it might have already been done automatically!
There’s nothing special about the Spectre/Meltdown patches; they are pushed out to computers in the usual way.
Here’s the quick ‘411’, there’s greater detail later on but here’s what you need to do.
Windows:
First and most important. If you have third-party anti-virus software, update it FIRST.
The Windows patch for Spectre/Meltdown will not install unless AV software has been updated. That’s to prevent serious ‘blue screen’ crashes of Windows after patching.
If you don’t have extra AV software (Windows Defender that comes with Windows 8/10 is enough) then you can update. More likely, Windows has updated for you.
Go to Settings | Windows Update and click the Check for updates’ button.

If any updates appear, let Windows apply them.
If, after checking for updates, you see ‘Your device is up to date’ then you’re done and can go back to playing Solitaire <g>.
Mac:
Go to App Store | Updates and check for updates.
Apple devices – iOS
Go to Settings and look for a new system update.
We go into detail below but really all you have to do is let the Windows/Mac automatic update process do its thing.
Performance Hit
There’s been talk about computers slowing down when the Spectre/Meltdown patches are applied. That’s quite plausible because the software workaround for hardware bugs take up system resources.
Early talk was of massive 30% slowdowns. Now Microsoft and others are saying that the slowdown won’t be that bad, but not giving any detail. Of course, it’s in those company’s interests to downplay any computer slowdown.
We’ll have to wait for independent testing to discover what the real level of performance hit is.
But the talk of computer slowdown is academic for most individuals and corporate users.
On balance, the risk from Spectre/Meltdown hacking is far greater than any hassle from a performance hit.
You should update all your computers/devices and live with any slowdown.
Managers of server farms and cloud storage will have to worry about performance issues. Even a slowdown of a mere 5% means more computers have to be added to make up the difference.
We hope that for individuals, the performance slow-down post-patches will be unnoticeable. There’s sure to be reports from people of slow computers after the Spectre/Meltdown patching but that might not be the real reason.
Windows 10
Microsoft says that is has released Spectre/Meldown patches, but you’d be forgiven for being uncertain.
Update Anti-Virus Software First
Firstly, update any ‘extra’ anti-virus software. The Windows patch for Spectre/Meltdown will not install unless AV software has been updated. That’s to prevent serious ‘blue screen’ crashes of Windows after patching.
The AV software update will add this registry entry.
Key="HKEY_LOCAL_MACHINE" Subkey="SOFTWARE\Microsoft\Windows\CurrentVersion\QualityCompat" Value="cadca5fe-87d3-4b96-b7fb-a231484277cc" Type="REG_DWORD"
Data="0x00000000"

Windows Update looks for that key and won’t apply the patch until it’s there. If you don’t have extra anti-virus software, then Windows will handle it for you. Windows Defender appears to be updated automatically, adds the necessary registry entry, then allows the Spectre/Meltdown patch to be applied. The above screen shot is from a machine with no extra AV software and the registry entry has been added.
More information is available at Microsoft. What’s notable about that page is the absence of any mention of Spectre or Meltdown.
To bring your computer up to date, go to Settings | Windows Update and force a check for updates.
A computer restart is required to apply the patch, so you might see this:

Close your regular programs then click Restart Now. The updating should only take a few minutes.
The above applies to the latest Windows 10 version 1709 or ‘Fall Creators Update’. If you’re running earlier versions of Windows 10 there’s are separate patches available.
- v 1703 (Creators Update): KB4056891
- v 1607 (Anniversary Update): KB4056890
- v 1511 (November Update): KB4056888
- v 1507 (Initial Release): KB4056893
Whichever version of Windows 10 you have, the update process is the same, as described above. Only the patch KB number is different.
Are you patched?
There are two ways to check if your computer has been updated. Either the Windows build number or look for a particular patch to have been installed.
Build Number
The build number is at Settings | System | About then scroll down to ‘Windows Specifications’.
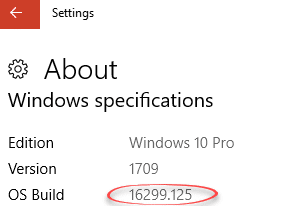
Look for OS Build 16299.125 or higher if you have Fall Creators Update.
Patch or KB reference
Alternatively, look for the patch labelled KB4056892 as installed on your computer. Go back to Settings | Windows Update and click on View installed update history.

Scroll down to the Quality Updates section (Microsoft Euphemism alert!) and look for KB4056892 (or alternative patch for earlier versions of Windows 10).

Windows 7
The instructions are fundamentally the same for Windows 7 except the interface and a name is different.
Back then, the Windows security option was called Microsoft Security Essentials. It’s available as a free, separate download.
Update MSE or any third-party anti-virus software first, then run Windows Update until there’s nothing left to update.
Windows XP
Microsoft will not update Windows XP, but they might, just might, change their minds. After all, there are many places still using Windows XP including, amazingly, British nuclear submarines.
Macs and iPads
Apple has good page explaining the problem and what they’ve done. Apple’s explanation is a lot better than the public statements from Microsoft.
“Apple released mitigations for Meltdown in iOS 11.2, macOS 10.13.2, and tvOS 11.2. watchOS did not require mitigation. Our testing with public benchmarks has shown that the changes in the December 2017 updates resulted in no measurable reduction in the performance of macOS and iOS as measured by the GeekBench 4 benchmark, or in common Web browsing benchmarks such as Speedometer, JetStream, and ARES-6.”
Updates have been pushed out for the current versions of MacOS for computers and iOS for devices. No mention of updates for past versions, most notably before ‘High Sierra’ for Macs.
On a Mac computer, the High Sierra release was patched in late December to version 10.13.2.
To check go to the Apple logo at top left | About this Mac and look for the version number:

The update to 10.13.2 requires a computer restart.
Browsers
Web browsers should also be updated. The updates are designed to block attempts to exploit Spectre/Meltdown using cunningly made web pages. This will help protect from hacking on operating systems that have not been updated.
Make sure your browser, Internet Explorer, Edge, Safari, FireFox, Chrome or whatever is updated.
Microsoft Office and Spectre/Meltdown
Similar to browsers, Office is a likely path of infection on computers. Despite all the warnings and protections, infected documents are opened and whole networks infected. Future malicious documents are likely to take advantage of Spectre/Meltdown bugs.
We hope Microsoft will add some Spectre and Meltdown coverage in the Office programs. This will add another layer of protection, especially on computers that have not been patched.
Anti-Virus software
All the AV software makers are releasing updates so you should update any security software you have.
We’ve said it many times, Windows has perfectly good security software in-built. Most people don’t need anything more than Windows Defender to protect themselves.
Virtual Machines
We’ve not seen any reliable discussion about the effect on virtual machine users. VM’s, liker Hyper/V or VMware, are commonly used by Microsoft Office users who need to run different versions of Office or need isolated development environments.
Windows 10 for Microsoft Office users has a long chapter devoted to Hyper/V in Windows 10. It explains what Virtual Machines are, explains the strange terminology and goes step-by-step through setting up your first Hyper/V with Windows and Office.
Virtual Machines and Spectre/ Meltdown
Certainly, the Host computer (the operating system running Hyper/V or VMware) should be updated asap – no question about that.
The ‘hypervisor’ or software that runs the virtual machines also needs to be updated. That means Hyper/V, VMware Workstation or other similar products.
The question seems to be if individual virtual machines should be updated as well. On that there’s no definite answer. According to experts, each client/guest VM does not need to be updated. Unless there’s a good reason not to, it would seem prudent to update guest operating systems anyway — “from an overabundance of caution” . That’s OK for people with a few VM’s but some organizations have hundreds.
Hyper/V and Spectre/Meltdown
Hyper/V should be updated as part of Windows Update. But Microsoft is being appallingly negligent in their support for Hyper/V customers. The best we could find was this forum page which has no official comment from Microsoft but speculation from well-meaning people.
VMWare Workstation and Spectre/Meltdown
VMware Workstation v14 is already protected (presumably VMWare had advance notice of the bugs and included fixes in v14, released in Sept 2017). Workstation v12 should be v12.5.8 or later. For more info and details on other Vmware products go here.
Chip Update / Firmware
Intel and other computer makers will be releasing firmware updates. These updates should patch the Spectre/Meltdown bugs at a deeper level which should be faster and more secure than operating system patches.
But firmware patches are complicated and take time to develop, test and deploy. So it might take weeks or months for those updates to come out. Even then, updating firmware is a bit harder than software updates and the consequences dire if the update goes wrong.
The true fix will be major changes to the CPU chips themselves. But that will take many years to develop, test, manufacture and sell.
In the meantime, we’ll have to rely on software, operating system and firmware updates.
Update Reliability
The big question about all these updates is … how reliable are they? Will the bug fixes work properly or even cause more problems.
Microsoft especially has a bad track record when it comes to faulty patches. Too many times, Windows and Office patches have caused more bugs than they tried to solve.
You might not have heard about these problems because Redmond is expert at covering up these gross mistakes with obfuscation, bordering on outright lying. A mostly pliant tech media helps Microsoft cover up their mistakes.
We’d not be surprised to see the Spectre/Meltdown patches being quietly updated to repair flaws in the update itself.
Those concerns should not, in our view, delay you from applying the patches. The oncoming risk is too great.
Cloud Computing
The big hit of Spectre/Meltdown is on cloud computing. Thousands, millions of servers across the globe need to be updated. The big cloud companies like Google, Microsoft, Amazon and many others are doing that as I type this.
The risk in cloud computing is that an infected server could, potentially, read private data from customers. That risk is low but possible.
For us cloud users, all we can do is trust our cloud service suppliers. Cloud computing requires a lot of trust by customers that the suppliers will be reliable, stable and honest.
Déjà vu – West Wing style
If you’re having a little Déjà vu about this tech story, you’re probably remembering an episode of The West Wing.
In ‘Enemies Foreign and Domestic’ there’s a sub-plot about a US computer maker which discovers a long-standing bug in their chips. IMDB Wiki The episode is also worth watching for a glorious little turn by the ever-reliable Ian McShane.
Insider Trading and Spectre/Meltdown
You can bet there’s going to be a close look at insider trading related to Spectre and Meltdown. Since the bugs where known inside major companies for five months, there’s the possibility that staff or executives sold off stock expecting a stock price drop when the news came out.
According to Axios, the first person to look at is Intel’s CEO Brian Krzanich. Mr Krzanich changed his automated stock selling program after the news of Spectre/Meltdown reached the company. In that change, the program was instructed to sell around $39 million of INTC stock, taking his stock holding to the minimum level he has to own.
Has Microsoft patched Spectre and Meltdown?
It sounds like a silly question … surely Microsoft has released a Windows update to cover Spectre and Meltdown? If you read Microsoft’s own documentation, you’d have second thoughts.
Here’s the fix list for KB4056892, it’s notable for what’s NOT mentioned.
“Key changes include:
- Addresses issue where event logs stop receiving events when a maximum file size policy is applied to the channel.
- Addresses issue where printing an Office Online document in Microsoft Edge fails.
- Addresses issue where the touch keyboard doesn’t support the standard layout for 109 keyboards.
- Addresses video playback issues in applications such as Microsoft Edge that affect some devices when playing back video on a monitor and a secondary, duplicated display.
- Addresses issue where Microsoft Edge stops responding for up to 3 seconds while displaying content from a software rendering path.
- Addresses issue where only 4 TB of memory is shown as available in Task Manager in Windows Server version 1709 when more memory is actually installed, configured, and available.
- Addresses issue where update installation may stop at 99% and may show elevated CPU or disk utilization. This occurs if a device was reset using the Reset this PC functionality after installing KB4054022.
- Security updates to Windows SMB Server, the Windows Subsystem for Linux, Windows Kernel, Windows Datacenter Networking, Windows Graphics, Microsoft Edge, Internet Explorer, and the Microsoft Scripting Engine. “
There’s no mention of Spectre or Meltdown in that bug fix list. It’s possible that the last item ‘Security Updates …’ is intended to cover these major problems but that’s speculation. An explicit mention of Spectre and Meltdown would reassure many Microsoft customers.
If you’re surprised by Microsoft’s lack of proper disclosure, then you’re not been in the mysterious and PR spin driven world of Microsoft updates. Experienced and exasperated Windows/Office users know that Microsoft always prefers obscurity and spin to honest and plainly worded disclosure. For the Spectre / Meltdown bugs, this is just Microsoft acting normally.
Nerdy Stuff
For those of you interested in the nerdy details.
The two bugs were discovered in July 2017 by Google Researchers who privately told Intel and other affected companies like Microsoft. That means developers have had about five months to develop updates. That’s good news because rushed updates are more likely to cause trouble.
Spectre affects all computer chips, not just Intel, so it’s a concern for all devices.
Spectre is really two vulnerabilities.
CVE-2017-5753 “Systems with microprocessors utilizing speculative execution and branch prediction may allow unauthorized disclosure of information to an attacker with local user access via a side-channel analysis.” or a ‘bounds check bypass’ for short.
CVE-2017-5715 has the same description but is known to it’s friends as a “branch target injection.”
Apple describes Spectre as “make items in kernel memory available to user processes by taking advantage of a delay in the time it may take the CPU to check the validity of a memory access call.”
Spectre is the more worrying of the two issues. It’s a bug at the very heart of chip design and it’ll take a lot of work to fix future chips. In the meantime, we’ll have to rely on software patches to, in effect, protect the chip from it’s vulnerability.
Meltdown affects only Intel chips. It’s a single bug called CVE-2017-5754 which also has the same description as the two Spectre CVE’s. The short name is “rogue data cache load.” and it lets a program directly read the kernel memory.