We won’t bore you with yet another article about today’s Petya ransomware attack We do have some notes and reassurance that arise.
Security Patches
Microsoft have this one covered.
Back in April 2017 they released relevant patches for Windows Vista and Windows 7, 8.1 and Windows 10 plus server editions
Also important patches for Office 2007, 2010, 2013 and 2016 plus Windows related patches for WordPad.
You should be protected if you’ve kept up to date with Windows/Office patches, even with a little delay. The organizations affected were not updating their systems as they should.
Run Windows Update and separate Office Update (if necessary), if you want to make sure.
Standard caution applies
Aside from the software patches, the usual cautious computer advice applies.
- Be wary of unexpected or unusual emails with strange attachments.
- In this case, an RTF document should be a hint that something might be awry.
- Anti-virus software should be kept up-to-date. For most people that means Windows Defender, which comes with modern Windows.
How Petya works
It infects a computer via a malicious RTF (Rich Text Format) document opened in Microsoft Office or WordPad. RTF files have been used to attack computers before and probably will be again.
Within a network, the virus spreads using a Microsoft file sharing system, SMBv1, which is why there are separate patches for Windows.
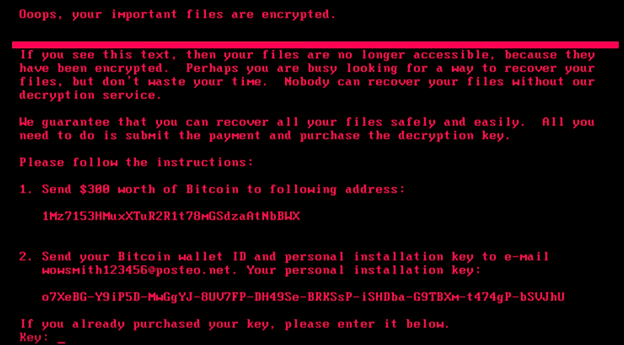
If you’re infected
You’ll need help. The email address for the blackmailers is disabled. There’s no way to get a recovery key (assuming they’d issue a key, even after paying).
Your computer reboots after infection, turn if OFF immediately. The ransomware does its encryption of your documents after a restart and posing as a CHKDSK scan of your hard drive. If you stop the encryption, there’s a chance of recovering your files and documents.
