There’s a simple trick to ensure that an email is real, not a phishing trick to get your personal information. But Microsoft makes it easy for phishing attacks to pretend that are the real thing..
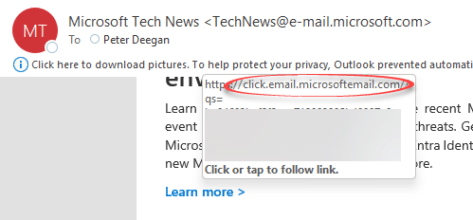
Hover over a link in an Outlook email to see the real url that you’ll visit if you click.
Look carefully at the domain name, right after the https:// . It should be the domain name of the legitimate company. For example, all the links in the Office Watch and Office for Mere Mortals newsletters use office-watch.com or click.office-watch.com . The ‘office-watch.com’ part means you know it’s from us.

Outlook shows the full email link in a tooltip when you hover the mouse pointer.
Ignore all the stuff after the domain name. Anything after the third / character is data sent to the web server, it doesn’t indicate the real domain owner.
Office-Watch.com has been recommending this simple trick for many, many years.
Use the best known domain
Ideally, all messages from a company use their main, popularly known domain. It’s a protection for the company and reassuring to customers.
Google and AirBnb do that, among many. Here’s examples from recent emails that use their main domain name.

But not Microsoft
Guess who doesn’t bother … yup, Microsoft. The company assures us (endlessly) that they give customer security their highest priority but they don’t bother with a simple protection against phishing.
Here’s a recent Microsoft email with links to microsoftemail.com which has no web site (an immediate red flag).
A Whois search confirms that the domain is owned by Microsoft, but it could easily be a fake.
That domain is a little better than a few years ago. Here’s the link from a real, past Office 365 email about file deletion. It’s a type of phishing email that’s commonly used by criminals to try getting into your Microsoft account login.
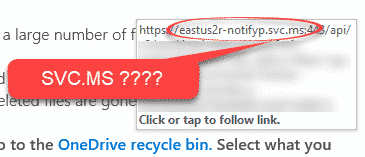
The domain they’re linking to is svc.ms which isn’t obviously a Microsoft domain and might not be.
.MS is the top level domain for the island of Montserrat, not Microsoft though the company does rent some .ms domains (aka.ms is a common one).
Svc.ms IS a Microsoft owned domain, but you must do a WhoIs domain ownership search to check that. We did that but regular Microsoft customers should not need to bother.
Using a browser to svc.ms or even the full https://eastus2r-notifyp.svc.ms:443 domain (used in Microsoft’s email above) is no help. At the least, Microsoft could put up a simple web page explaining their ownership of the domain and it’s use.
There’s nothing to stop someone registering a .ms domain name and we’ve done it!
OfficeWatch.ms
Anyone can use .MS Top level domain and to prove it, we registered OfficeWatch.MS it redirects to our main site.
Nothing to do with Microsoft, but unwary people might not realize that. Anyone can register a .ms domain and use it to fake Microsoft emails and links.
What must Microsoft do?
They should dump these obscure domain names in emails and use clear Microsoft.com subdomains.
Instead of click.email.microsoftemail.com or svc.ms Microsoft should use click.email.microsoft.com or svc.microsoft.com that’s a simple DNS mapping that would take seconds to do and perhaps a few minutes to sync across global DNS servers.
Shortlinks … why bother in emails
Microsoft is probably using .ms to make shorter web links but short links aren’t necessary in emails. Their domain links aren’t that short with the long sub-domain name and unnecessary port suffix (port 443 is the default for https).
On social media like Twitter, short links have a place. Like many companies, Office-Watch.com has it’s own short domain https://ofl.me for our Twitter and Facebook posts.
But they aren’t needed in emails. Email readers either click on links or, at worst, copy/paste a link.
Excel ‘system delay’ phishing trick
A different type of Office 365 phishing scam – by voicemail
Office 365 is #1 – for phishing and scamming