The WhatsApp security bug made a lot of headlines this week. As the virtual dust settles, what should you do and what is there still to worry about.
A company discovered a bug in WhatsApp which they packaged up and sold to various parties. The Pegasus bug allowed hacking of targeted individuals (mostly human rights lawyers and others that are ‘inconveniencing’ various governments). The hack is installed in an embarrassingly simple way, all the hacker had to do is make a WhatsApp call to the target! The receiver didn’t even have to answer the call for the spyware to be installed by WhatsApp onto the iPhone or Android device. Once installed, Pegasus gives access to most of the smartphone, not just WhatsApp data.
WhatsApp eventually discovered the bug in their system and moved to patch their software (see below).
What it means
WhatsApp, and many other companies including Microsoft, make a lot of noise about ‘end to end encryption’. They promote that the connection between you and the receiver is protected from spying.
That protection is important but is now ‘a given’ which all customers should expect.
The real problem is security at each end – not someone ‘listening in’ to the WhatsApp messages in transit.
Security boffins talk about ‘Data in Motion’ and ‘Data at Rest’.
In this case, the WhatsApp hack allowed others to read messages before or after the ‘end to end encryption’ has happened as well as other data on the device.
We were surprised that the targeted people were using WhatsApp at all. These are people who are rightly wary of spying from government agencies and we’d have thought they’d be much more careful than most.
WhatsApp is targeted by hackers for much the same reason that Microsoft Office is targeted. Both are very widely used and any vulnerability can be very profitable.
Beating Bots, Spies and Cock-ups
Beating Bots, Spies and Cock-ups is our guide to the many options for protecting your personal and business information from spying. WhatsApp is covered, in depth among other messaging services.
Some of our recommendations are:
- Use Signal, another messaging service which is, if anything, more secure and supports document transfer. Other services, like WhatsApp, use Signal’s encryption technology.
- Use multiple layers of security. Instead of sending text messages, send secure containers. It’s simple to make well-encrypted files that contained all sorts of details. If a hacker gets into your message, they must also unlock the files or documents. Beating Bots, Spies and Cock-ups has advice on making many types of secure containers, encrypting documents and PDFs with really complex passwords.
- Two factor authentication is important but WhatsApp does NOT have true ‘two-fac’ (despite advice in many reports of the last few days). WhatsApp merely a second password option that needs to be entered from time to time. That second password would not have protected people from the WhatsApp security breach. Office Watch has been pushing Two-Factor Authentication for many years and has a book about ‘two-fac’ for our supporters.
What to do – updating WhatsApp
You won’t find any mention of this security bug on the WhatsApp web site! Despite all the media coverage, their Blog is silent and there’s no mention of the bug fix in their version history for WhatsApp apps. This from a company which boasts that ‘Privacy and Security is in our DNA’.
WhatsApp say they have updated their apps to fix the security breach. For most Apple and Android users, they should already have the update, courtesy of automatic updating of their devices.
Android users need Version 2.19.137 or later.
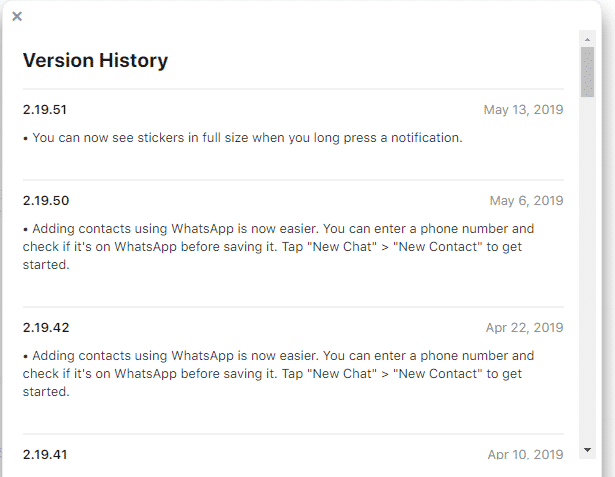
Apple / iOS users need v 2.19.51 or later though you’d not know that from the Version History on the iTunes store.