Fake login pages for Microsoft 365, OneDrive or Outlook.com are now the second most common phishing targets. Links in emails or messages to these bogus pages which grab your email and password for hackers to steal your secrets, or those of your company.
Ironside reports that Microsoft related fake login pages are only second to Paypal.
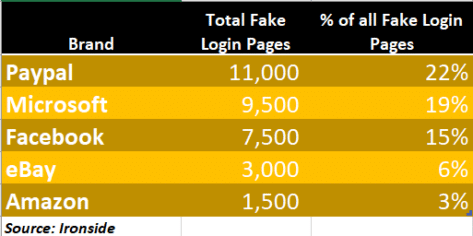
Arguably, stealing someone’s Microsoft account login can be more dangerous.
A personal Hotmail/Outlook.com email account can be used to hack into other accounts and gather lots of fodder for identity theft.
Corporate accounts open the door to a lot of private information about the company from email, SharePoint, OneDrive and Teams.
Criminals target certain types of organization like finance, healthcare tech and some government agencies. They can also focus on specific companies with very carefully worded emails that appear to be ‘in-house’.
What can you do to protect yourself?
You’re probably sick of hearing it, but Two-Factor Authentication is the best way to secure your email and other important accounts.
We strongly urge all Office Watch readers to use ‘2Fac’ on their major accounts. Email accounts, banks and major online shopping like Amazon.
Even if you’re tricked into entering your login name and password, the hackers can’t get into your account without the extra authentication code that only lasts a minute.
Checking for fake login links
A simple way to check a suspicious link is to look at the domain name used in the link – not the visible text but the real link.
We’ve noted before that most companies only use their main domain name for links. Anything from Google will use google.com etc.
But not Microsoft, which persists in using the .MS domain for many links in their emails. They’ve been doing this for a few years despite the risk to customers.
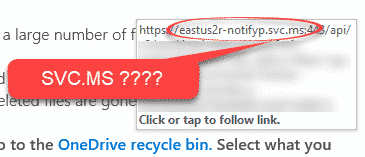
The .MS domain isn’t owned by Microsoft. Anyone can buy a .MS domain and we did just to show how easy it is, try https://officewatch.ms <g>.
Make sure an email link is real not phishing, why does Microsoft makes it easier for criminals?
Excel ‘system delay’ phishing trick
A different type of Office 365 phishing scam – by voicemail